PlaidCTF Zipper Forensics Writeup
This was a forensics challenge. We get a zip file named ziper.zip. Trying to extract it, we are greeted with an error message.
unzip zipper.zip
Archive: zipper.zip
warning: filename too long--truncating.
: bad extra field length (central)
So, there is something wrong with the filename length. Possibly in the central headers. A quick readup on how ZIP files are constructed from ForensicsWiki and Structure of PKZip File helped a lot in solving this particular challenge.
Opening up the zip file in wxHexEditor, started tagging all the necessary fields while reading the above linked resources. Managing to escape from getting lost in the sea of bytes, finally got something like this.
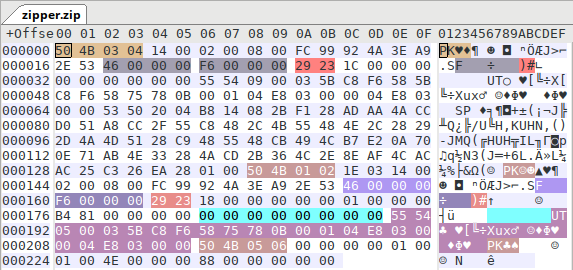
The red colored tags show the filename length field. They are of two bytes. So, they form a 16-bit integer stored in little-endian format. So, 0x2329 equals 9001 bytes which is impossible because, the entire file itself is only 236 bytes in size.
From the central directory file record header, by eliminating the sizes of all the other structures, we can calculate that the filename is only 8 bytes long. So, we change the bytes to 0x0800 in both the local file header and the central directory file header. Also, the filename field is filed with null bytes. So, replacing it by any printable ASCII characters, we would get the reconstructed zip file baclk.
Saving the patched copy of the zip file, extracting it we get a file with contents
Huzzah, you have captured the flag:
PCTF{f0rens1cs_yay}
Original File: zipper.zip
Patched File : zipper.patched.zip
TAGS file : TAGS